 An election campaigning website operated by Likud―the ruling political party of Israeli Prime Minister Benjamin Netanyahu―inadvertently exposed personal information of all 6.5 million eligible Israeli voters on the Internet, just three weeks before the country is going to have a legislative election via sloppy coding on it’s website.
An election campaigning website operated by Likud―the ruling political party of Israeli Prime Minister Benjamin Netanyahu―inadvertently exposed personal information of all 6.5 million eligible Israeli voters on the Internet, just three weeks before the country is going to have a legislative election via sloppy coding on it’s website.
This is extremely rare, and almost unheard of in Israeli software which is known as the most bulletproof in the world. Israeli cyber security research and technology was the world’s first and is incorporated in almost every cutting edge cyber-security product currently in use.
In Israel, all political parties receive personal details of voters before the election, which they can’t share with any third party and are responsible for protecting the privacy of their citizens and then delete it after elections are over.
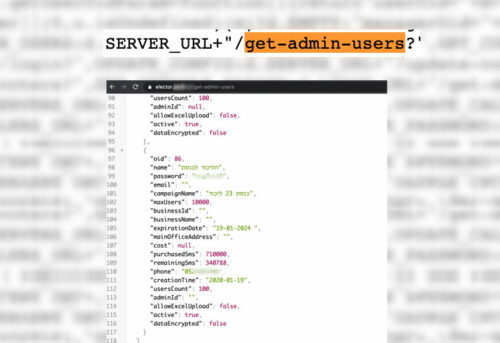
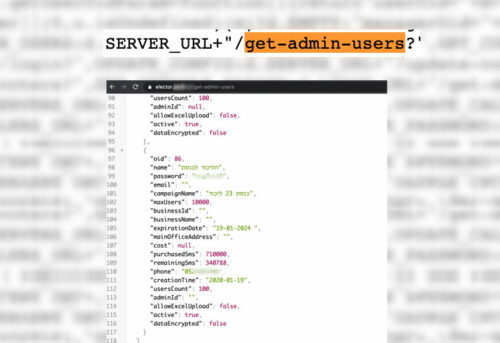
However, Likud shared the entire voter registry with Feed-b, a software development company, who then uploaded it to a public website (elector.co.il) promoting the voting management app called ‘Elector.’Ran Bar-Zik, a web security researcher, who disclosed the issue, said the leak was not due to any security vulnerability in the “Elector” app. Apparently the incident occurred due to negligence by the software company promoting themselves who leaked the username and password or the administrative panel through unprotected code that could be seen in any web browser by right-clicking on the page and selecting “View Page Source.” You could then see the link to the “get-admins-users” URL, where you could easily see the passwords of “admin” users (those with authorization to manage the database) from any browser.
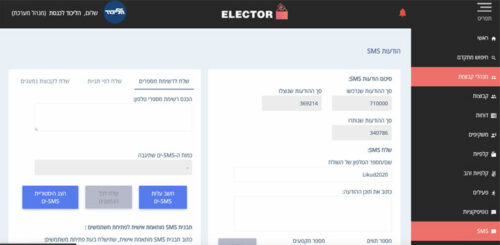
Here are a couple of screenshots of the app, one of which is shown while right clicked in page source mode:
 The exposed database includes the full names, identity card numbers, addresses, and gender of 6,453,254 voters in Israel, as well as the phone numbers, father’s name, mother’s name, and other personal details of some of them. The Elector website is now off-line until the software company has confirmed that the flaw has been patched. Best practice is to have the website code encrypted but that was not done in this case.
The exposed database includes the full names, identity card numbers, addresses, and gender of 6,453,254 voters in Israel, as well as the phone numbers, father’s name, mother’s name, and other personal details of some of them. The Elector website is now off-line until the software company has confirmed that the flaw has been patched. Best practice is to have the website code encrypted but that was not done in this case.
There is no way to know how many people have since then been able to download the voters’ database.
The Israeli Justice Ministry’s Privacy Protection Authority (PPA) said it is currently investigating the incident.

